Convert ldapdomaindump to Bloodhound
Convert ldapdomaindump to Bloodhound using ldd2bh
TL;DR
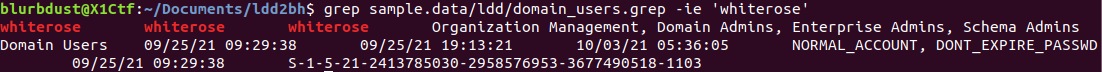
I was on a internal engagement without credentials but we got a successful relay to LDAP. We were able to dump information from LDAP but wanted to avoid changing or adding a new computer to the domain. I’m a little too used to the Max workflow and wanted to convert the ldapdomaindump data into Bloodhound data.
Disclaimers
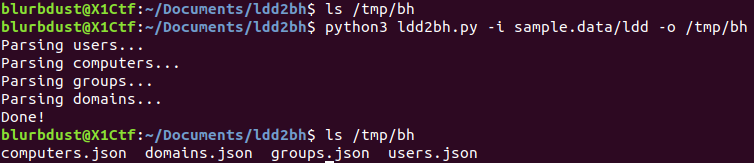
This tool is not fully fleshed out. It currently provides the bare minimum for getting usable objects within Bloodhound. Sometimes, the users.json file requires pretty printing before Bloodhound will upload the data. I have not figured that out and the engagement moved on from initial access so I ran out of time to polish this tool.
Another note worthy item is ldapdomaindump does not contain all of the ACLs that a Bloodhound collector would identify so that data is left blank for all objects.
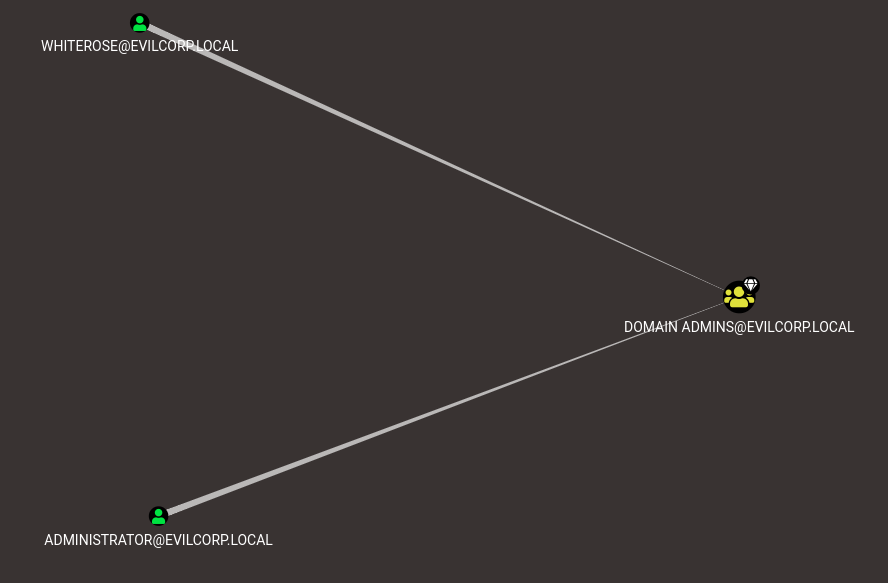
Currently Local Administrator access is assumed to all computer objects for Domain and Enterprise Admins. It’s likely correct but not a guarantee.
Useful Scenarios
This tool is very useful if you are on an internal and do not have credentials yet or prefer ldapdomaindump over a Bloodhound collector. It’s especially useful if you are accustomed to having Bloodhound data, like pretty graphs from Bloodhound, or really like Max’s workflow.
Isn’t there already one?
Well yes and no. There is one for the fist release of Bloodhound but it hasn’t and won’t be updated according to this Github issue. So I set out to make my own and I envisioned this as the successor to @dirkjanm/@_dirkjan’s already existing ldd2bloodhound converter.
Shoutouts
Shoutout to b1gbroth3r for providing the ldapdomaindump data from his homelab. Shoutout to knavesec for fixing bugs for me when I was being dumb.